DocuSign has admitted they were the victim of a data breach that has led to massive phishing attacks which used exfiltrated DocuSign information. Ouch. Especially given the level of trust they portray…
They discovered the data breach when on May 9, 15, and 17 DocuSign customers were being targeted with phishing campaigns. They now are advising customers to filter or delete any emails with subject lines like:
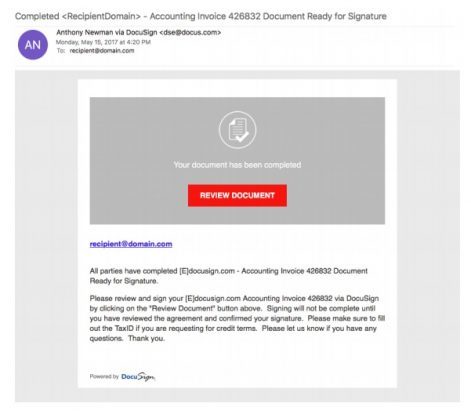
- Completed: [domain name] – “Wire transfer for recipient-name Document Ready for Signature”
- Completed [domain name/email address] – “Accounting Invoice [Number] Document Ready for Signature”
- Subject: “Legal acknowledgement for [recipient username] Document is Ready for Signature”
The campaigns all have Word docs as attachments, and use social engineering to trick users into activating Word’s macro feature which will download and install malware on the user’s workstation. DocuSign warned that highly likely there will be more campaigns in the future. Here is an example, these emails look very real:
Feel free to cut and paste this email through to friends and family to help keep them safe:
The campaigns all have Word docs as attachments, and use social engineering to trick users into activating Word’s macro feature which will download and install malware on the user’s workstation.
Hackers have stolen the customer email database of DocuSign, the company that allows companies to electronically sign documents. These criminals are now sending phishing emails that look exactly like the real DocuSign ones, but they try to trick you into opening an attached Word file and click to enable editing.
But if you do that, malware may be installed on your workstation. So if you get emails that look like they come from DocuSign and have an attachment, be very careful. If there is any doubt, pick up the phone and verify before you electronically sign any DocuSign email. Remember: Think Before You Click…
You can read more details about the hack here
If you would like to see advanced warnings of security threats (like this one) along with security tips to help keep you safe, drop you details into the form below: